File Encryption Solution Framework (FESF)
Facilitates the development of transparent, on-access, file-based encryption for Windows or Linux
Update: Version 2.0 Released 15 August 2025
The OSR File Encryption Solution Framework (FESF) allows Clients to incorporate transparent on-access, per-file encryption into their products. Adding on-access encryption to a product might sound like something that should be pretty simple to accomplish, on either Windows (using the File System Minifilter model) or on Linux. And while getting the basics to sort of work can be pretty easy, there are lots of edge-cases that cause a developing a reliable, interoperable, product to be seriously complicated. Creating a solution that performs well is even more difficult. Here at OSR we have been designing, developing and supporting file encryption “toolkits” and our clients’ successful implementations based on them for more than 20 years. If you’re developing a product that needs to implement file encryption for Windows or file encryption for Linux, you should check out FESF.
What kinds of products will FESF help you build? To name just a few:
- File and document security, management, and tracking for security and compliance
- Data loss prevention
- Document and file authentication
One of the main goals of FESF is to handle most of the necessary complexity, including the actual encryption operations, in OSR-supplied and OSR-maintained kernel-mode code. Policy determinations (such as which application instances get transparent encrypted/decrypted access to a given file) are all done in user-mode by implementing a few simple callbacks. This allows Clients that license FESF to build customized file encryption products with no kernel-mode programming. Let’s restate that for emphasis: FESF licensees can develop a per-file encryption solution – with all the stability, performance and security required by such solutions – entirely in user-mode. OSR has already done the kernel-mode programming for you.
FESF kits are available to support both Windows and Linux. Both implementations use the same on disk format, allowing seamless file sharing and interoperability. Both platforms feature very similar interfaces for user-mode policy determination and customization, and allow developers of FESF-based products to define metadata that is stored with each file.
The latest version of the FESF Solution Developer’s Guide is now online.
- Start With Best in Class Code — FESF provides all the infrastructure needed to demonstrate a working dynamic per-file encryption/decryption product. Starting with this code, your team adds the customization (such as unique user interface, encryption policy, and key management) that differentiates your product and provides your unique added value.
- Customization Entirely in User Mode — All the customization your team will need to perform can be done in user-mode, using the language of your choice. Of course, OSR is ready to help if your product requires extensive customization including changes to kernel-mode code.
- Encrypt Files Anywhere — Your policy can include encryption anywhere: On your local drive, on a server onsite or in the cloud, on a USB or other removable media device – wherever you like – and it just works.
- Flexible, Dynamic, Policy Determination — Your code is called whenever a new file is created or an existing encrypted file is opened. Your policy determines whether that particular open instance should result in raw or transparent encrypt/decrypt access. Your policy decision can be based on any number of factors including the file path or name being accessed, the accessing user’s credentials, and/or the accessing application. Policy can also be dictated by environmental factors such as time of day, the system on which the file resides, or whether the file is being remotely or locally accessed.
- Performance — An encryption solution has to be secure and it has to be reliable, that’s a given. And while customers are willing to accept some overhead for encryption operations, performance is certainly among the top issues with which per file encryption solutions struggle. That’s why engineering team members expended a great deal of effort designing performance into FESF from the beginning. From the on-disk structure, to a streamlined interface model to the way we’ve implemented the file system filtering: Performance was a number one goal.
- Efficiency — Encrypted files remain small, even including encryption header and key information.
- Interoperability — Everyone runs an anti-virus solution on their computer. Users expect an encryption solution to “play well” with whatever other software they have running on their machines. FESF for Windows was designed using the Isolation Filter approach, based on the “same stack” file system filter model OSR pioneered back in the mid-90s and that is officially endorsed by Microsoft. The result: Dramatically increased interoperability with all types of other file system filters.
- Multi-Platform Support. This is a vital part of building products these days: customers want to share data between their devices, regardless of the OS. Full-featured versions of FESF are available on both Windows and Linux. Code libraries that support encrypting or decrypting individual file on other platforms (where FESF is not installed) is included. We are actively looking to expand the native platforms that FESF supports, so if there’s a specific platform you need, feel free to contact us.
- Microsoft Certified Solution. The components of FESF have passed applicable Windows Hardware Lab Kit (HLK) tests allowing your resulting solution to gain access into Windows Hardware Compatibility Program for certification and distribution via Windows Update.
- One-time License Fee – NO Royalties. In addition to the broad terms of licensure, FESF is licensed for a one-time fee, and you may ship your product to end users anywhere in the world without royalties.
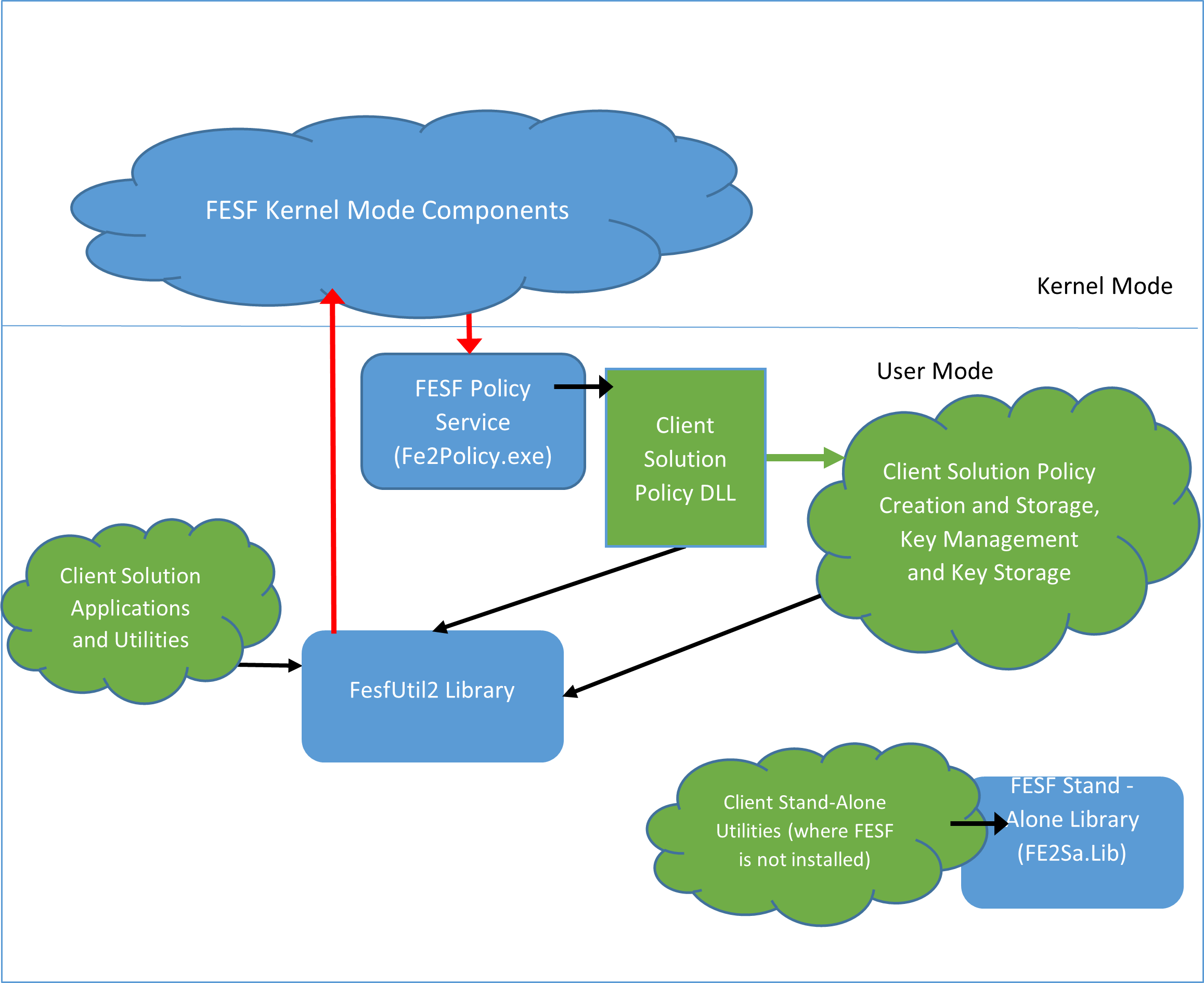
FESF for Windows User-Mode Components
- FESF Policy Service. The FESF Policy Service is the interface between FESF and the Client’s components that determine policy. The FESF Policy Service receives requests from the FESF Kernel Mode Components, converts them to the expected format, and passes them to the Client-developed Policy DLL.
- FESF Policy DLL. The Policy DLL is the primary interface point between FESF and the Client’s product implementation. OSR includes a sample Policy DLL that Clients can use as the basis for their own implementation, including making decisions on policy and key management.
- FESF DS Service. The FESF Data Storage Service provides services to Client-developed utilities. These services include determining if a file is encrypted, checking the true size on disk of an encrypted file, updating the header, etc.
- Other Applications/Utilities. These are modules that may be designed and implemented as part of the client-specific end-user product.
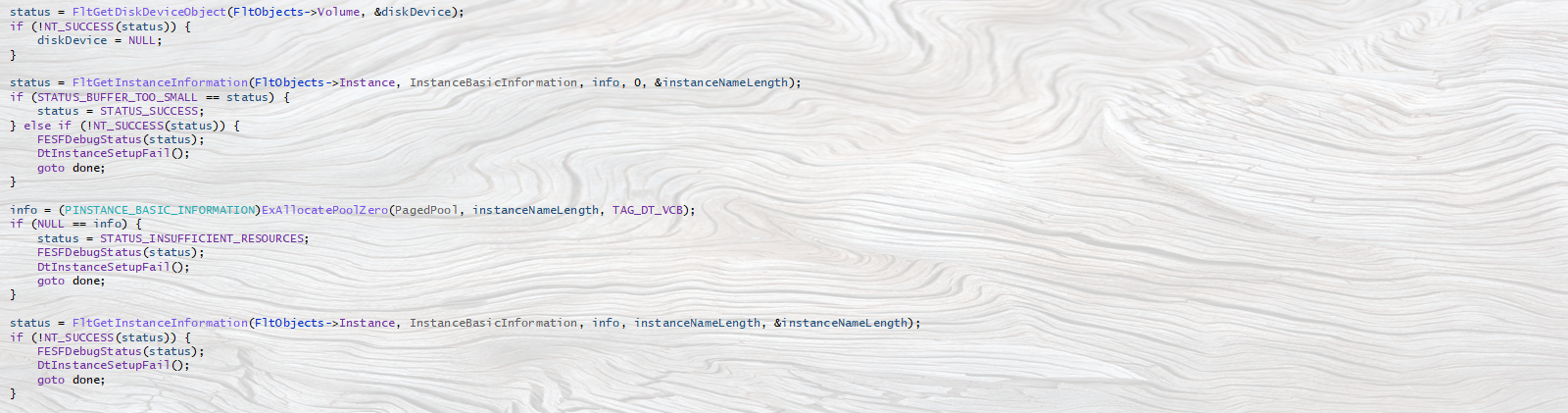
FESF for Windows Kernel Components
The FESF Kernel Mode Components are responsible for intercepting file operations (such as CreateFile, ReadFile, and WriteFile) on supported file systems, implementing Client-specified policies, managing provision of the correct “view” (encrypted/decrypted or raw) of a given file’s data based on the Client-specified policy, and also for performing the actual encryption/decryption operations via Microsoft’s CNG kernel-mode library. The kernel components comprise a series of file system mini-filters and their associated libraries.
FESF provides the following features:
- Transparent on-access encryption of newly created files and transparent on-access encryption/decryption of FESF encrypted files, all under the control of Client-defined policy.
- Same stack “Isolation”. On Windows FESF uses an in-line isolation filter to control the cache and manage clear and encrypted views of data. In Linux, FESF is implemented as a kernel-mode layered file system.
- Client policy determination (that is, deciding which files get encrypted and which accesses to encrypted files receive raw access or transparent encryption/decryption access) in user-mode using Client-provided components. These components include a Policy DLL, written in C/C++, plus any other combination of services, applications and utilities which may be written in any language that can communicate with the Policy DLL.
- Easy to understand samples that can be used by Client as a starting point to develop a complete Client Product.
- FIPS compliant encryption. The FESF utilizes the US FIPS 140-2 compliant Microsoft CNG libraries, customizable by the Client for implementing encryption and key storage providers.
- Cross-platform support. FESF is supported on both Windows and Linux. In addition, libraries for encrypting and decrypting individual files (in the absence of having FESF installed) are provided.
FESF for Windows OS Support
- 64-bit (X64) architectures of Windows 10 (1607) and later; Windows Server 2016 and later.
- 64-bit ARM architectures of Windows 10 (1904) and Server 2025 and later
FESF for Linux OS Support
- RHEL 8 and later (including CentOS equivalents) — The SELinux module is also fully supported.
Technical Support
FESF licenses include one (1) year of technical support, including questions, bug support, and access to framework maintenance updates. Licensees will also have options to secure major updates (functional enhancements) and OS upgrades as well.
Windows Distribution Kit
- Source code for all user-mode components including the user-mode FESF Service.
- Documentation, headers, and library files necessary for Client to interface with OSR-supplied FESF user-mode components.
- Object code for all other FESF components (source licenses to KM components by special arrangement).
- All code is written in C/C++ with binaries built using the Windows Driver Kit and Microsoft’s Visual Studio.
Resources
- FESF “Evaluation Edition” allows you to work with and test FESF, even prototype your product, at no cost in limited non-production environments.
- Other architecture and API documentation available; please contact the OSR Sales Team for more details.
Customized Development
Some FESF licensees may wish to customize core components of FESF to meet their product needs. In addition to providing options for licensure of FESF kernel components, OSR can be engaged to provide turnkey custom development services to modify FESF components to client specifications.
Free FESF Evaluation Edition
To help you evaluate the features of FESF within your own solution, OSR offers the free FESF for Windows Evaluation Edition. This edition provides the full suite of FESF components and source code to the user-mode FESF for Windows Solution Sample (and project files), which can be customized by licensees under an limited, non-commercial license arranged with the OSR sales team.
As opposed to a simple demonstrable evaluation, this edition will allow you to undertake actual development of your solution without having to commit to a full FESF license up front. This Evaluation Edition license also includes an option for limited, external distribution for the purposes of demonstration (e.g., to prospective investors or end-customers).
Contact the OSR Sales Team for more details.
FESF for Linux, Too!
Native support for FESF is available on Linux, as well as on Windows. The two implementations are fully interoperable at the file level, allowing encrypted files to be exchanged seamlessly between systems.
Our Linux implementation is new kernel-mode implementation, not merely a “port” of FESF for Windows, to ensure compatibility and performance. The user-mode interfaces that are used to determine whether a particular fopen operation get transparent encryption/decryption or sees raw data are very similar between Windows and Linux. This makes it easy to implement cross-platform products using FESF.
More specific information on FESF for Linux can be found here.